«Дух неонацистской сегрегации»: в России осудили позицию Франции по вакцинам
Прослушать новость Остановить прослушивание Михаил Терещенко/ТАСС Представитель МИД России Мария Захарова осудила «дискриминационные высказывания» госсекретаря МИД Франции Клемана Бона, критиковавшего другие государства…
Читать далее «Дух неонацистской сегрегации»: в России осудили позицию Франции по вакцинам«Бессмысленный фарс»: Украина намерена депортировать россиян из Крыма
Прослушать новость Остановить прослушивание Константин Михальчевский/РИА «Новости» Рано или поздно произойдет «деоккупация» Крыма и россиян нужно будет депортировать с территории полуострова, заявил…
Читать далее «Бессмысленный фарс»: Украина намерена депортировать россиян из КрымаУсловный Запад против России: что ждать от выборов в Молдавии
Прослушать новость Остановить прослушивание Гавриил Григоров/ТАСС В Молдавии проходят досрочные парламентские выборы.
Читать далее Условный Запад против России: что ждать от выборов в Молдавии«Новые факты подлога»: в России указали на нестыковки в «отравлении» Навального
Прослушать новость Остановить прослушивание Alexey Malgavko/Reuters Техсекретариат Организации по запрещению химического оружия сообщил, что направил группу экспертов для оказания помощи Германии в…
Читать далее «Новые факты подлога»: в России указали на нестыковки в «отравлении» Навального«Наемники хотят убить его мечту»: вдова президента Гаити рассказала о гибели мужа
Прослушать новость Остановить прослушивание Жовенель и Мартин Моиз Жовенель и Мартин Моиз Dieu Nalio Chery/AP В соцсетях опубликована аудиозапись заявления Мартин Моиз…
Читать далее «Наемники хотят убить его мечту»: вдова президента Гаити рассказала о гибели мужаКазаков возьмут в Росгвардию
Прослушать новость Остановить прослушивание Виталий Тимкив/РИА «Новости» Казаки должны стать территориальным подразделением Росгвардии.
Читать далее Казаков возьмут в РосгвардиюПоворот на Запад: о чем говорят итоги выборов в Молдавии
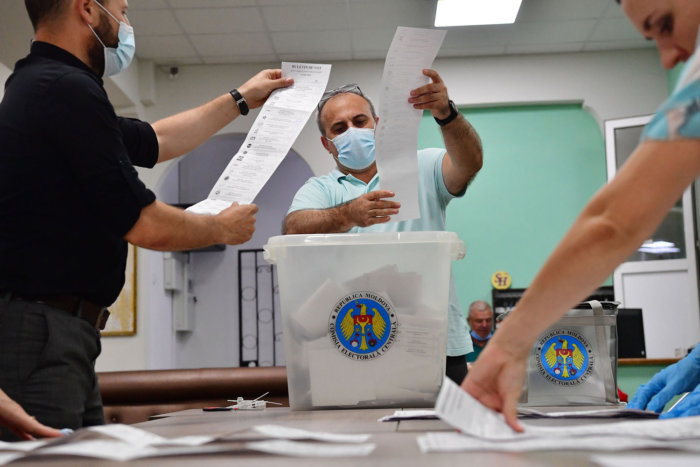
Прослушать новость Остановить прослушивание Подсчет голосов на избирательном участке № 1/109 в Кишиневе во время досрочных парламентских выборов…
Читать далее Поворот на Запад: о чем говорят итоги выборов в Молдавии«Верить их обещаниям недальновидно»: каким будет Афганистан при талибах*
Прослушать новость Остановить прослушивание Depositphotos Перспектива перехода власти в руки талибов** сегодня становится все более реальной с учетом того, как быстро переходят…
Читать далее «Верить их обещаниям недальновидно»: каким будет Афганистан при талибах*«Во времена холодной войны ничего подобного не было»: как изменились шпионские игры
Прослушать новость Остановить прослушивание Depositphotos Задержание в Санкт-Петербурге эстонского консула Марта Лятте породило волну слухов о начале новой шпионской войны, которая по…
Читать далее «Во времена холодной войны ничего подобного не было»: как изменились шпионские игры«Враги США»: зачем Украина преследует собственных граждан
Прослушать новость Остановить прослушивание Markus Schreiber/AP СНБО Украины согласовал введение санкций против 100 украинцев, которые находятся в списках США.
Читать далее «Враги США»: зачем Украина преследует собственных гражданПервый диалог после саммита: о чем говорили Путин и Байден
Прослушать новость Остановить прослушивание Президент России Владимир Путин и президент США Джо Байден во время встречи в рамках…
Читать далее Первый диалог после саммита: о чем говорили Путин и Байден«Тотальный дефицит»: на Кубе начались протесты из-за голода
Прослушать новость Остановить прослушивание Reuters США предостерегли власти Кубы от насилия в отношении протестующих кубинцев.
Читать далее «Тотальный дефицит»: на Кубе начались протесты из-за голода